Технология Variti
Мы не блокируем IP
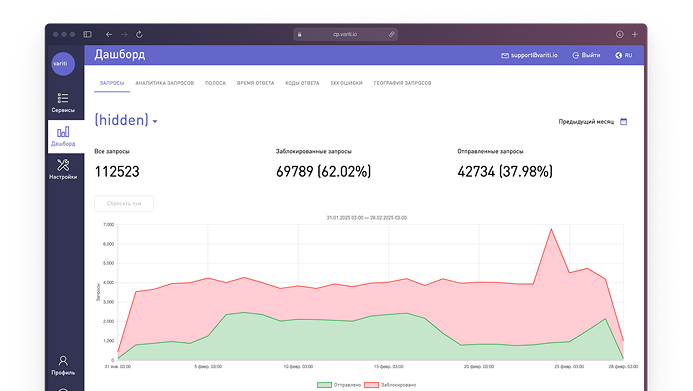
Мы блокируем только отдельные вредоносные автоматические запросы, а не целые IP-адреса. Это гарантирует, что все легитимные запросы, поступающие с тех же IP-адресов, не будут затронуты, и ваши пользователи получат доступ к вашему ресурсу из корпоративных и публичных сетей даже когда на ваш сайт идет серьезная DDoS-атака.
Проверяем каждый запрос
Алгоритмы Active Bot Protection обнаруживают и останавливают как единичные запросы ботов, так и массивные бот-атаки на сетевом уровне (L3–L4) и на уровне приложений (L7). Это значит, что ни одна кибератака не останется незамеченной, какой бы маломощной или хитроумной она ни была.

Работаем в режиме реального времени
Наша технология обеспечивает мгновенную защиту в режиме реального времени, начиная с самого первого запроса. Нам не нужно тратить время на первичный сбор данных, чтобы начать полноценно защищать ваши ресурсы.


Вписываемся в существующую инфраструктуру
Защиту Active Bot Protection очень легко установить: это не требует дополнительной настройки ваших процессов, инфраструктуры или политик безопасности.
Используйте нашу технологию для себя
Защита от парсинга
предотвращение автоматизированного копирования контента и сбора данных
Защита от DDoS
предотвращение атак, направленных на отказ в обслуживании вашего ресурса
Защита от сканирования
предотвращение атак, направленных на выявление слабых мест ресурса
Защита от кражи данных
предотвращение несанкционированного доступа и утечки конфиденциальной информации
Защита от ботов
блокировка вредоносных ботов, которые выполняют автоматизированные атаки
Защита от парсинга
предотвращение автоматизированного копирования контента и сбора данных
Защита от DDoS
предотвращение атак, направленных на отказ в обслуживании вашего ресурса
Защита от сканирования
предотвращение атак, направленных на выявление слабых мест ресурса
Защита от кражи данных
предотвращение несанкционированного доступа и утечки конфиденциальной информации
Защита от ботов
блокировка вредоносных ботов, которые выполняют автоматизированные атаки
Защита от поддельных учетных записей
предотвращение атак, направленных на имитацию деятельности легитимных пользователей в системе.
Защита от скальпинга
предотвращение атак, направленных на захват товаров, пользующихся повышенным спросом.
Защита от несанкционированного доступа
Аутентификация и авторизация (OAuth, JWT, API-ключи).
Защита от взлома учетных записей
предотвращение атак, направленных на несанкционированное получение доступа к учетной записи пользователя
Защита от перебора учетных данных
предотвращение атак, направленных на выявление валидных пар логин/пароль из утекших баз с персональными данными
Защита от брутфорса
увеличение задержки между попытками ввода пароля, блокировка простых и популярных комбинаций
Предоставляем услуги по модели SaaS
Быстрое и простое подключение
Не требует тонкой настройки
Соответствие PCI и GDPR

Аудит безопасности
Мы проводим индивидуальные нагрузочные тесты для проверки безопасности вашей инфраструктуры. Вы можете выбрать как простые, так и более сложные многоступенчатые симуляции атак. В итоговом отчете мы укажем все уязвимости и слабые места в вашей системе безопасности и предложим варианты защиты.